Cyber-Physical Security Systems
Cyber-physical security systems integrate computation, networks, and physical processes into a single operational fabric. They demand risk-aware, systemic defenses that consider sensor integrity, actuator timing, and firmware trust. Secure-by-design evolves into resilient postures through threat modeling, real-time monitoring, and automated containment. Governance and supply-chain discipline shape ongoing improvements across people, processes, and technology. The challenges are pervasive and interconnected, inviting steady scrutiny as threats evolve and defenses adapt. The next question concerns how these elements align in practice.
What Is Cyber-Physical Security and Why It Matters
Cyber-physical security refers to protecting integrated systems where computation, networking, and physical processes interact. This discipline evaluates vulnerabilities across layers, emphasizing resilience, governance, and risk-aware design. By treating cyber physical operations as a coupled enterprise, it clarifies how security architecture shapes defenses, recovery, and trust. It enables informed freedom, balancing innovation with systematic safeguards against cascading, real-world disruptions.
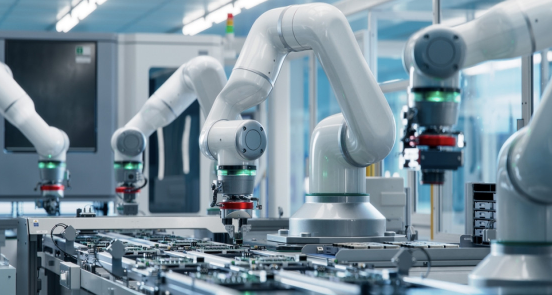
Core Attack Surfaces in CPS Environments
Industries deploying cyber-physical systems face a set of common, high-impact attack surfaces that arise from the intersection of computation, networks, and physical processes. Core attack surfaces include sensor deception threatening sensors integrity, actuator timing vulnerabilities that disrupt control loops, network exposure enabling eavesdropping or tampering, and firmware weaknesses that undermine trust. A disciplined, systemic risk view informs proactive mitigation.
Designing for Security: From Secure-by-Design to Resilience
Designing for security in cyber-physical systems requires moving beyond merely secure-by-design principles toward a resilient posture that persists under adverse conditions.
The analysis integrates threat modeling and risk quantification to anticipate failure modes, while governance alignment ensures accountability and policy coherence.
Prepared incident playbooks codify response play, recovery sequencing, and continuous improvement across systems, human operators, and supply chains.
Monitoring, Detection, and Response in Real Time
Real-time monitoring, detection, and response operate at the nexus of observable system state and actionable intelligence, enabling promptly verifiable insights into anomalous behavior across cyber-physical interfaces.
The approach emphasizes risk-aware, systemic assessment, leveraging real time telemetry to detect deviations and trigger automated containment, containment validation, and coordinated response, while preserving freedom through principled, transparent decision pipelines.
Frequently Asked Questions
How Does CPS Security Differ Across Industries and Sectors?
Differences across industries arise from varied threat landscapes and regulatory pressures; sector specific standards shape controls and risk appetites, while governance, auditing, and incident response evolve with each domain, demanding rigorous, risk-aware, systemic engineering for freedom-loving operators.
What Are Practical Cost Considerations for Implementing CPS Security?
Cost considerations shape CPS security; implementation timelines constrain risk. Juxtaposition: urgent alarms vs. patient budgets. The approach remains risk-aware, rigorous, systemic, balancing cost considerations with resilience, scalability, and governance, enabling freedom-focused stakeholders to pursue secure, adaptable deployments.
How Do Safety and Security Trade-Offs Affect System Design?
Safety trade offs shape system design, balancing resilience and performance as stakeholders pursue security optimization amid uncertain threats; design choices reflect risk-aware accountability, ensuring freedom to operate while trade-offs, margins, and contingencies govern overall safety and robustness.
Can AI Automate Threat Hunting Without Compromising Safety?
An allusion evokes cautious hope: AI automation can aid threat detection, yet safety remains paramount; automation must be bounded. The system benefits from rigorous risk assessment, clear governance, and layered controls to protect freedom while advancing threat detection.
See also: Reliable Tech System 218440672 For Growth
What Are Common Legal and Regulatory Implications for CPS Security?
Common legal and regulatory implications for CPS security include mandatory legal compliance and frequent regulatory audits, with risk-aware, rigorous considerations shaping governance. The detached observer notes systemic obligations that balance safety, freedom, accountability, and evolving compliance frameworks.
Conclusion
Cyber-physical security demands a systemic, risk-aware stance that treats cyber and physical domains as an integrated ecosystem. Secure design must evolve into resilient operations, with continuous monitoring, rapid detection, and automated containment. A failure in one layer tests the entire chain, underscoring governance, supply-chain integrity, and timely response. Example: a water treatment plant incident where sensor spoofing caused valve misoperation, mitigated only by cross-domain anomaly detection, redundant sensors, and coordinated incident command.




