Cybersecurity Best Practices for Businesses

Cybersecurity for businesses demands a risk-driven, scalable baseline aligned to goals. Start with robust data access controls and clear role-based permissions, paired with strong password hygiene. Implement integrated detection, response playbooks, and threat hunting to shorten dwell time. Emphasize phishing awareness, data governance, and comprehensive logging for audits. Continuous improvement through post-incident reviews and resilient recovery plans will shape how an organization handles the next challenge. The path to trust hinges on disciplined execution and informed prioritization.
What Cybersecurity Risk Should Every Business Expect?
One cybersecurity risk all businesses should anticipate is the constant threat of targeted ransomware and credential-stuffing attacks, which exploit weak access controls and stolen authentication data to disrupt operations, demand payment, or exfiltrate sensitive information.
Organizations pursue data encryption and phishing awareness as core defenses, aligning strategic risk management with freedom to innovate while preserving trust, resilience, and operational continuity.
How to Build a Solid Security Baseline for All Teams
A solid security baseline for all teams starts with a clear, minimal set of controls that align with business goals and risk appetite, then scales with interaction patterns and data sensitivity. Teams implement security governance and layered controls, balancing autonomy with accountability. Incident logging is standardized for rapid detection, audit trails, and continuous improvement, ensuring resilient collaboration while preserving freedom and strategic risk posture.
How to Protect Data With Access Control and Awareness Training
Access control and awareness training form a two-pronged defense: restrict data access to the minimum necessary and continuously educate users on risk-aware behaviors. The approach emphasizes data governance and role based access to assign permissions precisely, while enforcing password hygiene.
Phishing awareness programs reinforce vigilance, reducing credential theft. This combination sustains resilient operations without stifling organizational freedom.
How to Detect, Respond, and Recover From Threats Quickly
Threat detection, rapid containment, and swift recovery hinge on an integrated, repeatable playbook that minimizes dwell time and preserves business continuity.
The approach emphasizes Threat hunting to identify anomalies, Incident playbooks to guide containment, and data denial techniques to limit exfiltration.
A disciplined, risk-aware posture enables rapid decision-making, reduces impact, and sustains operations with intentional, freedom-oriented resilience.
Frequently Asked Questions
What Are the Most Common Cybersecurity Myths in Small Businesses?
Myth vs reality reveals that small business myths misjudge threats and costs; assuming cyber risks are external or manageable internally is erroneous. Small business myths overlook layered defenses, ongoing training, and incident response, risking complacency and costly, preventable breaches.
How Often Should We Perform External Security Audits?
The frequency of external audits should align with risk, regulatory demands, and business changes; conduct at least annually, with additional assessments after major incidents or significant scope expansion. Emphasize scope of third party assessments to identify residual exposures.
Which Cybersecurity Metrics Matter Most to Leadership?
The most important cybersecurity metrics for leadership center on cyber risk and data privacy, signaling trends in exposure, potential loss, and regulatory impact; they enable strategic decisions, risk-aware budgeting, and informed tolerance for freedom-oriented operational flexibility.
What’s the Cost-Benefit of Vendor Risk Management?
The cost benefits of vendor risk management depend on reducing third party risk exposures, incident costs, and regulatory penalties; strategic investment in vendor security yields measurable risk reduction and resilience, aligning risk appetite with governance, compliance, and freedom to operate.
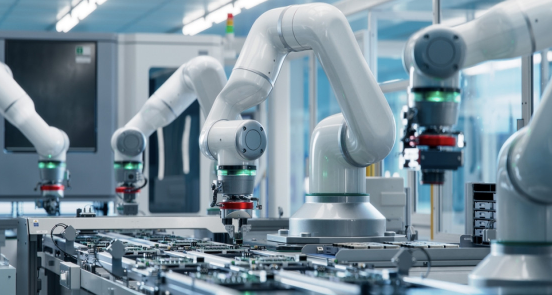
See also: Cyber-Physical Security Systems
How Can Remote Workers Stay Secure Without Productivity Loss?
Remote work security minimizes risk while preserving freedom: they implement identical safeguards, identical monitoring, identical policies; they balance access controls and training, balance device management and VPN use, balance incident response and user autonomy, balance productivity impact.
Conclusion
In this landscape, cybersecurity is the quiet referee of business ambition, not its antagonist. By establishing a measured baseline, clarifying access with purpose-built controls, and embedding awareness into daily practice, organizations can deter stormy threats before they rise. The playbook—detect, respond, recover—keeps the scene orderly, while post-incident learning rewrites the script toward resilience. Like a steady lighthouse in shifting seas, disciplined governance and continuous improvement guide ventures safely to trusted horizons.