Cyber Resilience Explained

Cyber resilience integrates people, processes, and technology to anticipate and withstand threats while preserving value. It blends prevention with rapid recovery and adaptive defense, shifting from static protection to dynamic risk management. This approach informs governance, investments, and real-time response, focusing on continuity and learning. Leaders weigh trade-offs between prevention and resilience, aiming for steady operations under pressure. The implications touch every stakeholder and demand disciplined execution as threats evolve. The conversation starts where plans meet practice.
What Cyber Resilience Really Means for a Business
Cyber resilience for a business is the ability to anticipate, withstand, recover from, and adapt to cyber threats while maintaining operations and protecting value.
This mindset guides leadership to map critical processes, quantify risks, and invest in agile defenses.
It minimizes disruption, preserves stakeholder trust, and reduces business impact, enabling confident experimentation and strategic growth within an ever-evolving threat landscape.
How Resilience Differs From Traditional Cybersecurity
Resilience broadens the focus beyond traditional cybersecurity by emphasizing continuity and adaptability across people, processes, and technology. It treats safeguards as dynamic capabilities, not fixed defenses.
The distinction centers on risk vs. recovery: preparedness accepts residual risk while prioritizing rapid restoration.
Threat tolerance guides decisions, balancing preventive controls with adaptable response, ensuring resilient operations amid evolving threats and uncertainty.
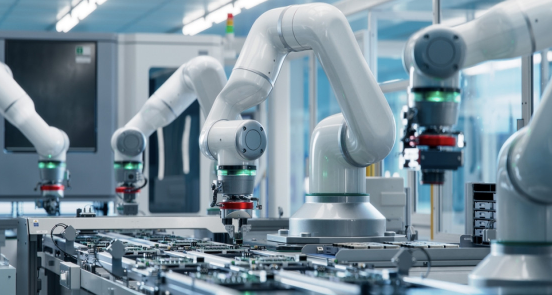
Building Blocks: People, Processes, and Technology for Resilience
Effective resilience hinges on three interdependent pillars—people, processes, and technology—each reinforcing the others to sustain operations under stress. The analysis emphasizes people readiness as a core capability, ensuring calm, informed action when disruption arises.
Process automation streamlines decision cycles, reduces error, and frees minds for strategic judgment.
Together, these elements enable proactive, adaptable resilience without compromising organizational freedom or agility.
From Plan to Practice: Incident Response, Architecture, and Continuous Learning
To move from planning to action, organizations must align incident response, architecture, and continuous learning into a cohesive, repeatable workflow. Within this framework, incident response capabilities surface in real time, guided by a lucid architecture strategy that scales. Continuous learning embeds feedback into governance, shaping organizational culture toward proactive risk management and resilient, freedom-forward decision making.
Frequently Asked Questions
How Do You Measure Cyber Resilience ROI Over Time?
ROI tracking quantifies cyber resilience ROI over time by mapping incident cycles to financial impact, dashboards, and risk-adjusted gains. It feeds Board level metrics, guiding strategic decisions in a risk-aware, proactive manner for a freedom-minded audience.
What Board-Level Metrics Reflect Resilience Performance?
Like a compass, board-level metrics reflect resilience performance: board governance effectiveness, budget alignment, continuous improvement progress, risk communication clarity, and incident recovery velocity; they guide strategic risk posture, enabling proactive, risk-aware decisions and freedom to adapt.
How Should Resilience Integrate With Privacy and Compliance?
Resilience integration requires aligning controls, data governance, and incident planning with privacy alignment principles; the approach is risk-aware, strategic, and proactive, enabling freedom-borne decisions while ensuring legal compliance, stakeholder trust, and robust breach-response coordination across functions.
Which Tools Best Quantify Detection-To-Recovery SLAS?
Tools that quantify detection-to-recovery SLAs emphasize detection latency and recovery efficacy, enabling risk-aware, strategic planning. They enable proactive freedom-seeking organizations to monitor, compare, and optimize resilience programs through transparent, iterative measurement and governance.
See also: easytonet
How Do You Simulate Resilience Without Disrupting Operations?
Simulating resilience without disrupting operations is achieved via nonintrusive testing and controlled simulations, yielding simulated downtime insights. A risk-aware, strategic approach enables proactive planning, preserving freedom to operate while validating recovery capabilities under real-world constraints.
Conclusion
In the evolving battlefield of digital risk, resilience stands as a quiet navigator guiding enterprises beyond mere defense. It alludes to a ship that learns from each storm, adjusting sails of people, processes, and technology to endure—and rebound—faster. The approach foresees threats, embeds rapid recovery, and treats disruption as data for improvement. By weaving governance with adaptive practice, organizations cultivate steadiness amid uncertainty, promising continued value while remaining vigilant, proactive, and strategically resilient.